System Architecture
Built on open standards for flexibility, scalability, and best-in-class cost-performance
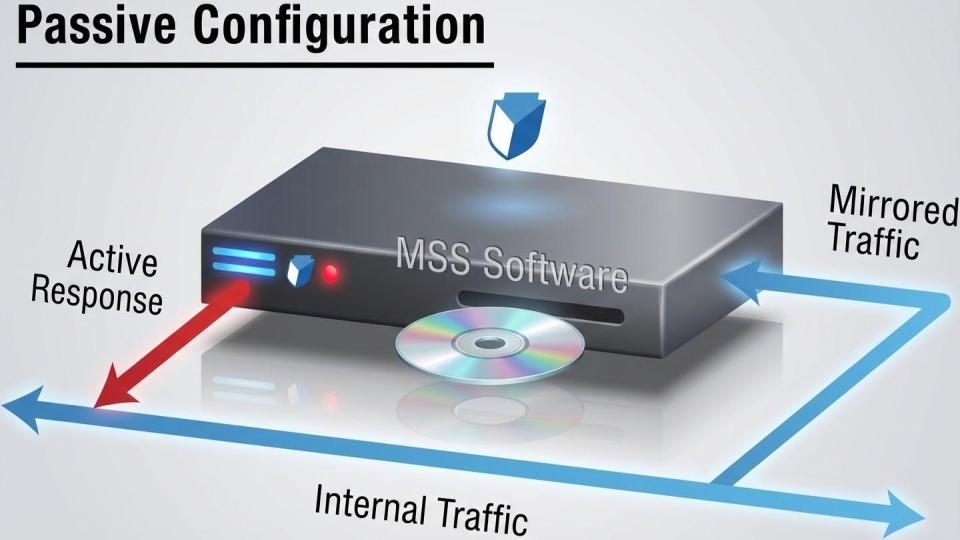
The MetaFlows Security System uses a distributed architecture with two main components: sensors and controllers. A single controller can manage anywhere from 1 to 1,000+ sensors, providing centralized management and analysis at any scale.
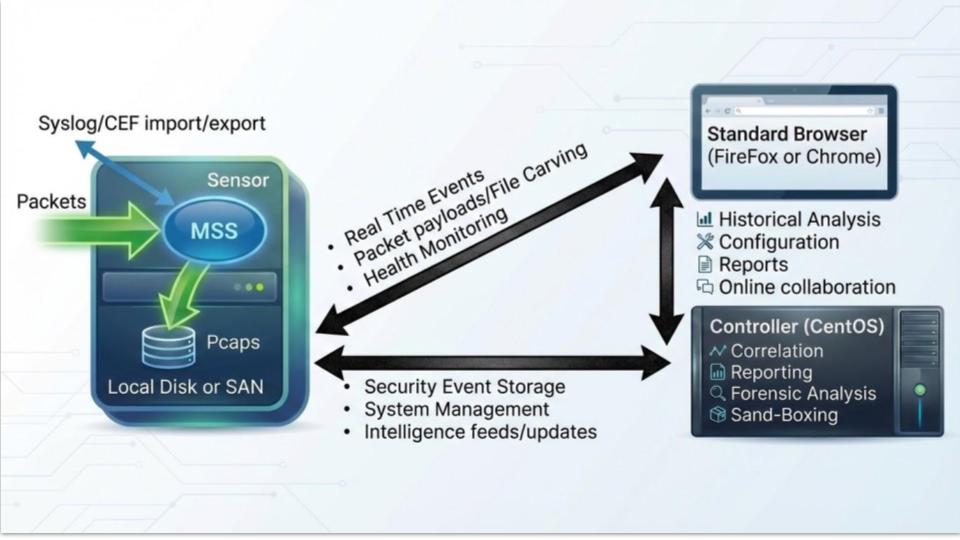
Distributed sensor and controller architecture
Sensors
Sensors run on standard Linux (CentOS or RHEL) augmented with our multi-functional deep packet inspection software and proprietary kernel drivers. Key features:
- Full root access: Easily augment with site-specific applications or configurations
- Automatic updates: OS updates via standard package management, MetaFlows software self-updates
- Flexible deployment: Install on customer hardware, VMware, or EC2 instances
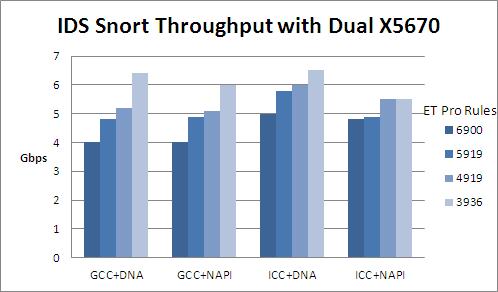
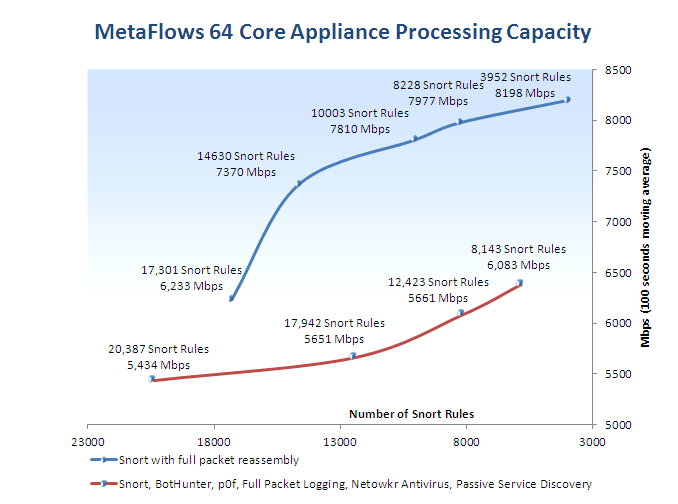
- High performance: Scales to 10 Gbps using PF_RING technology
Controller
The controller provides centralized management and analysis capabilities:
- Web GUI for system management of all sensors
- Receives and stores metadata continuously exported by sensors
- Web-based forensic analysis application
- Automated reports and email alerts
- Security intelligence feed management and distribution